Binance founder Changpeng Zhao, widely known in the crypto community as CZ — amplified a warning this week that deserves a wider audience. The post he shared came from a crypto developer who goes by bigpey on X, and it describes one of the cleaner examples yet of how artificial intelligence is being used to run social engineering scams, the kind where the deception is literally a convincing human face on a video call, not even a suspicious link or a bad email.
Social engineering refers to manipulation tactics that exploit human trust rather than technical vulnerabilities. No code gets cracked. Instead, the attacker builds enough credibility to get the target to hand over access themselves.
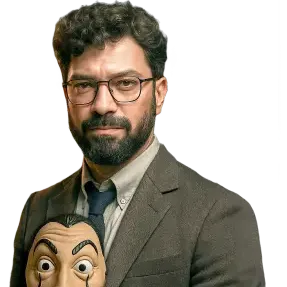
Bigpey’s account of what happened is worth reading in full. Someone reached out to him posing as Pierre, a contact from the Cardano Foundation he had spoken with before, a real person, a real prior relationship.
The request was plausible: a call to discuss a project called Atrium. Bigpey accepted. A Microsoft Teams invite arrived. He joined the call. Pierre’s face was there. His voice was there. Two other apparent Cardano Foundation staff members were on the call as well.
Then the call started lagging. A message appeared saying his Teams software needed updating. It directed him to install the new version through Microsoft’s command-line terminal, a tool called PowerShell that gives software installation instructions directly to a computer’s operating system.
He followed the instructions, caught himself, and shut his laptop down immediately when he realized something felt wrong. “I now think this was AI,” he wrote, referring to the faces and voices on the call. “As someone who is quite technically savvy, I just got cooked.”
He rescheduled the call to Google Meet. The attacker, apparently unable or unwilling to replicate the deepfake setup on a different platform, claimed to be busy and asked to move the meeting. That’s when the full picture became clear.
CZ’s repost came with a pointed caption: “Watch out for hacks like these.”
AI has removed the last reliable check
What makes bigpey’s account significant isn’t that he was careless. He wasn’t. He had a prior relationship with the person being impersonated. He had spoken with him before, including on video. And yet he was deceived for long enough that his laptop was almost certainly compromised before he shut it down.
The old mental checklist for spotting a scam, does this person look right, sound right, do I recognize them, no longer works when AI can generate a convincing face and voice in real time. Google’s Mandiant security unit has previously documented threat actors using AI to fabricate deepfake images and videos, allowing attackers to pose as trusted participants in video calls.
The goal, as analysts describe it, is to move past traditional phishing and create an environment where a victim has no reason to question who they’re talking to. The Cardano impersonation attack fits this pattern almost precisely.
It targeted an existing relationship, mimicked a known contact’s appearance and voice, staged a plausible pretext for the call, and used the resulting trust to deliver a malicious software installation.
This is not an isolated technique. Earlier this month, a threat actor identified as “Jinkusu” was reported to be selling cybercrime tools built around deepfakes and voice manipulation, specifically designed to bypass Know Your Customer checks at banks and crypto platforms. KYC, or Know Your Customer, refers to the identity verification process financial institutions use to confirm who they’re dealing with.
Tools that can fake that process at scale represent a different category of threat from individual scam calls. The broader numbers make the timing of bigpey’s warning especially relevant. The crypto industry lost over $606 million to hacks and exploits in the first 18 days of April 2026 alone, 3.7 times the total stolen across the entire first quarter.
Two incidents drove the bulk of that figure: a $293 million breach at Kelp DAO, a liquid restaking protocol, exploited through a vulnerability in the LayerZero cross-chain messaging system, and a $285 million attack on Drift Protocol on Solana executed through a sophisticated oracle manipulation. Both were linked to North Korean state-affiliated actors.
Zerion, a crypto wallet provider, disclosed on April 15 that a prolonged social engineering campaign tied to the same North Korean hacking cluster had successfully extracted around $100,000 from its hot wallets. The dollar amount is small compared to the protocol-level breaches.
What to actually do
Security researchers have been direct about what these attacks demand from ordinary users. CertiK senior blockchain investigator Natalie Newson has warned that AI is raising both the speed and the believability of attacks, with tools now capable of generating convincing deepfakes and scanning smart contracts autonomously for exploitable weaknesses.
“There are now more convincing deepfakes, autonomous attack agents, and ‘agentic AI’ that can autonomously scan smart contracts for bugs, draft exploit code and execute attacks at machine speed,” she said.
Her practical advice: verify URLs and smart contract addresses independently before interacting with them, and keep assets not in active use in cold wallets, hardware devices that hold private keys offline, away from any internet connection.
The US Treasury’s Office of Cybersecurity and Critical Infrastructure Protection announced in April 2026 that it would expand its threat identification program to cover digital asset companies, a signal that the scale of the problem has moved far enough up the priority stack to draw institutional attention.
Zooming out, bigpey’s takeaway applies regardless of how technically fluent you are: treat software installation requests from any call, meeting or message as a hard stop. If someone on a video call is asking you to run a command on your own machine, that is the moment to hang up, verify the person’s identity through a separate channel you control, and start from scratch.
Lag on a call that then prompts a software update is most likely not a coincidence. The face on the screen means nothing anymore. Also, the old saying if it sounds too good to be true, then it probably is, still stands.