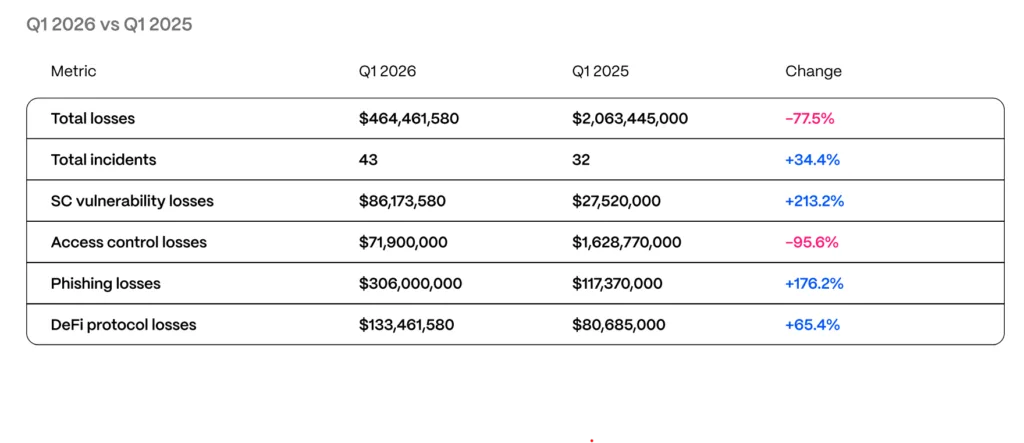
The numbers from the first quarter of 2026 tell a story that the Web3 security industry has been dreading for a while now. Blockchain security firm Hacken tracked $464.5 million in losses across 43 incidents between January and March, a figure that looks almost modest compared to the carnage of Q1 2025, but only because last year had the Bybit breach, a $1.46 billion outlier that skewed the entire annual picture.
Strip that away, and the underlying trend is unsettling in the sense that attacks are getting more targeted, more human, and harder to audit your way out of. Phishing and social engineering led the damage, accounting for $306 million of the quarter’s total.
A single hardware wallet scam in January was responsible for $282 million of that, roughly 81 cents of every dollar lost in Q1 came from one attack. Smart contract exploits added another $86.2 million, and access control failures, covering things like compromised private keys and misconfigured cloud services, drove an additional $71.9 million in losses.
Yev Broshevan, chief executive and co-founder at Hacken, put it plainly by mentioning that the most expensive failures these days “happen outside the code layer entirely.”
Where the actual damage is coming from
That observation carries a lot of weight when you start walking through the specific incidents. Step Finance was hit for $40 million after a North Korea-linked group used a fake venture capital call to gain access which appears to be a social engineering play
Resolv Labs suffered a $25 million breach tied to an AWS key management service compromise. Truebit lost $26.4 million to a bug sitting in a Solidity contract that had been deployed roughly five years ago, which raises its own uncomfortable question about how much legacy code is quietly waiting to be exploited.
Venus Protocol was taken down by a donation attack, an exploit pattern that security researchers had already documented as far back as 2022. Perhaps the most counterintuitive finding is that six audited protocols collectively lost $37.7 million. Resolv had been through 18 separate audits. Venus had five different firms sign off on it.
That doesn’t mean audits are useless, they clearly catch plenty of things, but it does suggest that audit coverage has started to give some protocols a false sense of completeness. Higher total value locked (TVL) projects draw more sophisticated attackers, and those attackers are increasingly going after the infrastructure surrounding contracts rather than the contracts themselves.
The North Korea thread runs through a significant chunk of Q1’s damage. Hacken flags DPRK-linked clusters as the most consistent operational threat in the space right now, connecting Step Finance’s $40 million loss and a separate breach at Bitrefill to a playbook that involves fake VC outreach, malicious video call tooling, and compromised employee endpoints.
According to Chainalysis data, North Korean groups extracted roughly $2.04 billion from the broader crypto sector across all of 2025, a figure that makes the Q1 2026 incidents look like continuation.
Their methods have also evolved. Beyond embedding IT workers inside target firms, DPRK-linked operators have started flipping the model, impersonating recruiters and engineering fake hiring pipelines specifically to harvest credentials and VPN access from employees at their current employers.
Regulators are paying attention… finally
The shift in where attacks are landing has not gone unnoticed by regulators. In Q1, the European Union’s Markets in Crypto-Assets Regulation and Digital Operational Resilience Act moved deeper into active enforcement, raising the bar on continuous security monitoring and incident response requirements.
Dubai’s Virtual Assets Regulatory Authority tightened its Technology and Information Rulebook. Singapore introduced Basel-aligned capital requirements alongside one-hour incident notification rules. The UAE’s new Capital Market Authority assumed federal digital asset oversight with expanded enforcement powers and steeper penalties.
Hacken connects those frameworks to what it calls a new benchmark for “regulator-ready” stacks which are daily proof-of-reserves reconciliation, 24/7 on-chain monitoring across treasury wallets and privileged roles, automated circuit-breakers on minting and governance functions, and incident notification systems calibrated to the strictest applicable local standard.
The firm’s report puts forward both realistic and aspirational response benchmarks. Realistic targets include detection within 24 hours, threat labeling within four hours, and blocking within 30 seconds, while aspirational goals push that all the way down to 10 minutes for detection and a one-second block threshold.
Whether the industry moves fast enough to meet those benchmarks is an open question. The pattern across Q1 audited projects still getting hit, legacy code still running, state-sponsored groups still finding their way in through employee laptops and fake Zoom calls suggests that writing secure code, while necessary, has become somewhere close to table stakes. The harder work is everything that surrounds it.